Security is not a feature.
It is a
forecast.
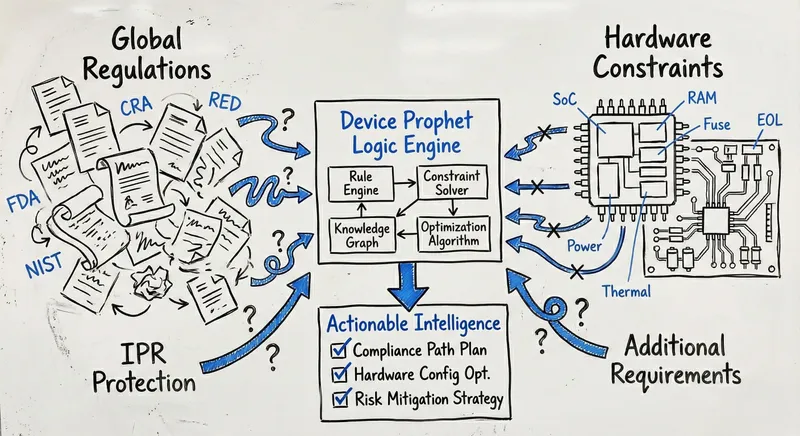
Device Prophet is a specialized security lab built by architects who were tired of the "Compliance Guessing Game."
Our Mission
Predict risks. Protect IPR. Secure your future.
We turn complex
regulations and security threats into clear, actionable intelligence
- so you can build with confidence.
Who We Are
Boutique Expertise. Founder-Led.
Device Prophet is not a generalist IT agency. We are an independent, specialized expert system and consultancy focused exclusively on the intersection of Embedded Engineering and Regulatory Compliance.
We operate as a lean, high-expertise unit. While our core team is agile, we are backed by a senior network of embedded developers and security engineers. This structure allows us to offer the personalized attention of a boutique consultancy with the technical depth of a large firm - without the overhead.
Our Philosophy
Why We Built the Prophet
For years, we worked as security architects for hardware companies. We saw the same expensive pattern repeat itself: excellent engineering teams being blindsided by compliance requirements (like the CRA or RED Art 3.3) only months before launch.
We realized that spreadsheet security doesn't work. The complexity of mapping 50+ evolving global regulations to thousands of potential hardware combinations is too much for a human to track manually.
We tried to find a tool that could predict these roadblocks during the design phase. We found only:
- Certification Labs: Too expensive and too late (post-prototype).
- Code Scanners: Too focused on software bugs, missing the architectural flaws.
So, we built Device Prophet. We replaced "gut feeling" with a deterministic Expert System. We don't guess if your device is compliant; we map your specific architecture against the rigid logic of the law.
Our Expertise
Grounded in Architecture, Not Just Compliance.
When you engage with our Expert Services, you are trusting your roadmap to professionals with the highest level of industry accreditation. Our methodology is not just about checking boxes; it is grounded in:
Certified Security Architecture
We approach every project with the rigor of a lead architect, applying principles of Defense in Depth from the very first whiteboard session. We understand that one size does not fit all: we clearly distinguish between what is strictly required for regulatory compliance and what is needed to make a device truly secure. Whether you need a cost-effective baseline or a hardened high-assurance design, we perform rigorous Threat Modeling to identify fundamental architectural flaws - such as weak trust boundaries or insecure logic flows - before they become expensive technical debt.
Cloud & Embedded Fusion
We bridge the gap between silicon constraints and modern cloud security. We ensure your architecture seamlessly integrates On-Device Key Storage (using Secure Elements or TEEs) with modern Cloud Platform Interaction. From establishing a Trusted Identity at the factory to securing encrypted Communications and daily Operations, we protect the entire data path.
Deep Engineering Experience
We understand that resources are always constrained and the Bill of Materials (BOM) matters. We don't just quote standards; we optimize for them within your cost and performance budget. We have lived through the reality of Legacy Updates forced by sudden Chip EoL, and we know the practical challenges of implementing Secure Boot and Secure Firmware Upgrades (OTA) without bricking a fleet. We provide advice that is technically feasible, minimizing the risk of a costly PCB respin.
Stop Guessing. Start Predicting.
Whether you are a startup validating a prototype or an enterprise managing a fleet, we help you see the future of your device.